When we talk about small or medium enterprises, they are on the verge of development. Many small and medium enterprises are gambling big in the global market and making a dominant stand in the market with their unique marketing skills and their unique set of products. There are various companies that have initiated with an innovative set of business strategies and made a stiff ground in the ground. However, in the modern era, availability of internet is such an important necessity that the conventional methods of business have been left far behind. Technology has completely changed the business strategies being adopted and the various business methodologies being implemented as well. However, these technological capabilities, when accompanied by internet services poses a great threat, since there are various external threats which may be harmful for the integrity of the small and medium businesses. For this purpose, various government and private services which are termed as IASME Governance are set in place. IASME Cyber Assurance (ICA) is an information assurance standard which holds a rather simple and sustainable working, which may be feasible for small and medium enterprises in order to pertain the cyber security of these enterprises.
 IASME Cyber Assurance (ICA) was originally made as an academic SME partnership and is widely liked by decision-makers, especially within the coast of UK and the small business companies working within UK. IASME Cyber Assurance (ICA) policies are mostly aligned with the Cyber Essential schemes which have been set in place by the UK government. One interesting thing regarding IASME Cyber Assurance (ICA) is that it does not possess any certain unique characteristic, since most of the policies defined by IASME Cyber Assurance (ICA) are relative to the international standards community, which include Plan-Do-Check-Art (PDCA) and Information Security Management Systems (ISMS). Both these standards communities are defined for an effective business terms to be intact and are recognized by major organization, both large and small enterprises. While generating various policies for IASME Cyber Assurance (ICA), the major reference source was small businesses, mostly allocated in the West Midlands of UK which showed a surprisingly positive result of the effectiveness of IASME Cyber Assurance (ICA) procedures. However, it is to be noted that the IASME Cyber Assurance (ICA) procedures are not only refined to small businesses. They are applicable to all sorts of organizations of varying scale. Moreover, these protocols are not restrained by geological factors as well, since these policies are defined based upon past community standards, therefore, it is safe to say that these procedures can be utilized in every region. It plays an important role in contributing to a larger sum of the supply chain of small businesses. With the passage of time, IASME Cyber Assurance (ICA) has become a major focus for various SMEs, since advancing times have required various security protocols to be set in place for maintaining the integrity of the small businesses since they are opting for allocating their business on the internet and the internet is filled with threats and malware which may compromise the future of the businesses. Security threats to businesses working in UK tends to increase and this poses vulnerability to the systems being used by the companies, which may result in breach of expensive data and systematic failures which may be devastating for the business owners. IASME Cyber Assurance (ICA) has maintained its protocols while keeping in view the intensity of the threats and the posed alarming higher concentration of external threats that pose a risky situation for cyber businesses to be intact.
IASME Cyber Assurance (ICA) was originally made as an academic SME partnership and is widely liked by decision-makers, especially within the coast of UK and the small business companies working within UK. IASME Cyber Assurance (ICA) policies are mostly aligned with the Cyber Essential schemes which have been set in place by the UK government. One interesting thing regarding IASME Cyber Assurance (ICA) is that it does not possess any certain unique characteristic, since most of the policies defined by IASME Cyber Assurance (ICA) are relative to the international standards community, which include Plan-Do-Check-Art (PDCA) and Information Security Management Systems (ISMS). Both these standards communities are defined for an effective business terms to be intact and are recognized by major organization, both large and small enterprises. While generating various policies for IASME Cyber Assurance (ICA), the major reference source was small businesses, mostly allocated in the West Midlands of UK which showed a surprisingly positive result of the effectiveness of IASME Cyber Assurance (ICA) procedures. However, it is to be noted that the IASME Cyber Assurance (ICA) procedures are not only refined to small businesses. They are applicable to all sorts of organizations of varying scale. Moreover, these protocols are not restrained by geological factors as well, since these policies are defined based upon past community standards, therefore, it is safe to say that these procedures can be utilized in every region. It plays an important role in contributing to a larger sum of the supply chain of small businesses. With the passage of time, IASME Cyber Assurance (ICA) has become a major focus for various SMEs, since advancing times have required various security protocols to be set in place for maintaining the integrity of the small businesses since they are opting for allocating their business on the internet and the internet is filled with threats and malware which may compromise the future of the businesses. Security threats to businesses working in UK tends to increase and this poses vulnerability to the systems being used by the companies, which may result in breach of expensive data and systematic failures which may be devastating for the business owners. IASME Cyber Assurance (ICA) has maintained its protocols while keeping in view the intensity of the threats and the posed alarming higher concentration of external threats that pose a risky situation for cyber businesses to be intact.
IASME Cyber Assurance (ICA) standards have kept in mind the following factors while determining the protocols to be set for SMEs:
- Managing security of the SMEs
- Information assets that need to be kept integrated while determining cyber security of SMEs.
- Cloud services which may be enabled for SMEs to be utilized. It is important to note that the modern era is mostly relative to the usage of cloud services, hence, the availability of cloud services is important.
- Managing risks that may be posed to SMEs when determining the online business strategies and identifying these risks and providing a proper protocol in order to tackle these risks effectively.
- Protecting sensitive data of SMEs, including financial reports, transactions and other sensitive information, which may be utilized by external threats for their personal gain, hence, posing a negative effect on the SMEs.
- People included in the SMEs and their identity, addresses etc.
- Security policy which may be set in place to determine a properly maintained SME.
- Physical environment in which the business may run, including the varying trends.
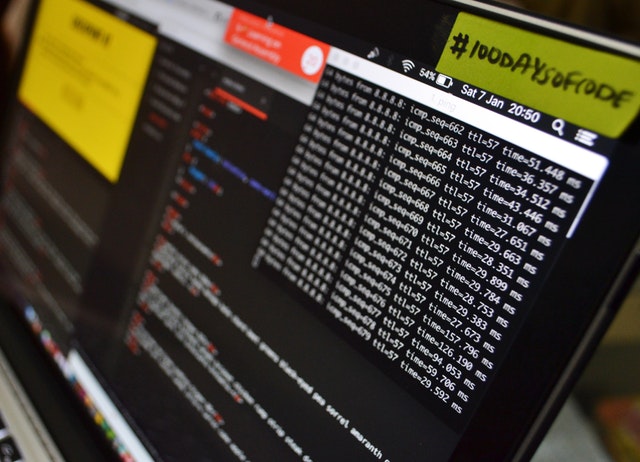
- Firewalls and internet gateways which may be utilized by SMEs for their online business. It is important to note that in order to protect SMEs from online threats, it is important to construct a strong firewall to disable the malicious threats from penetrating into the data and transaction processing of SMEs.
- Secure configuration of various software and technological components, which may be able to maintain the security measures set in place for the SMEs.
- Patches and upgrades in order to save the companies from upgrading malwares and threats.
- Operations being run and their management, which may include the cloud configuration that has been set in place for the companies.
- User accounts which need to be enabled for accessing data relative to the company, which may allow encrypted access to various personnel to this data, hence, maintaining the security protocols of the company.
- Administrative access to the data available on cloud regarding the company to certain certified administrative personalities.
- Protecting companies from malware on the internet which may cause systematic failure and damage the business of the SMEs.
- Determining the vulnerability posed to the companies.
- Monitoring various policies, including cloud configuration and upgrading security measures.
- Backing up data, in case a certain or all data may be lost
- Incident management in order to maintain the company’s business in case of emergency posed.
- Business continuity regardless of the restraints due to environment
All these policies play an important role in determining a proper maintained business for SMEs to effective carry out their business and allow a better output while maintaining the security measures, which is important in the growing risky situations posed to business pertaining online businesses.